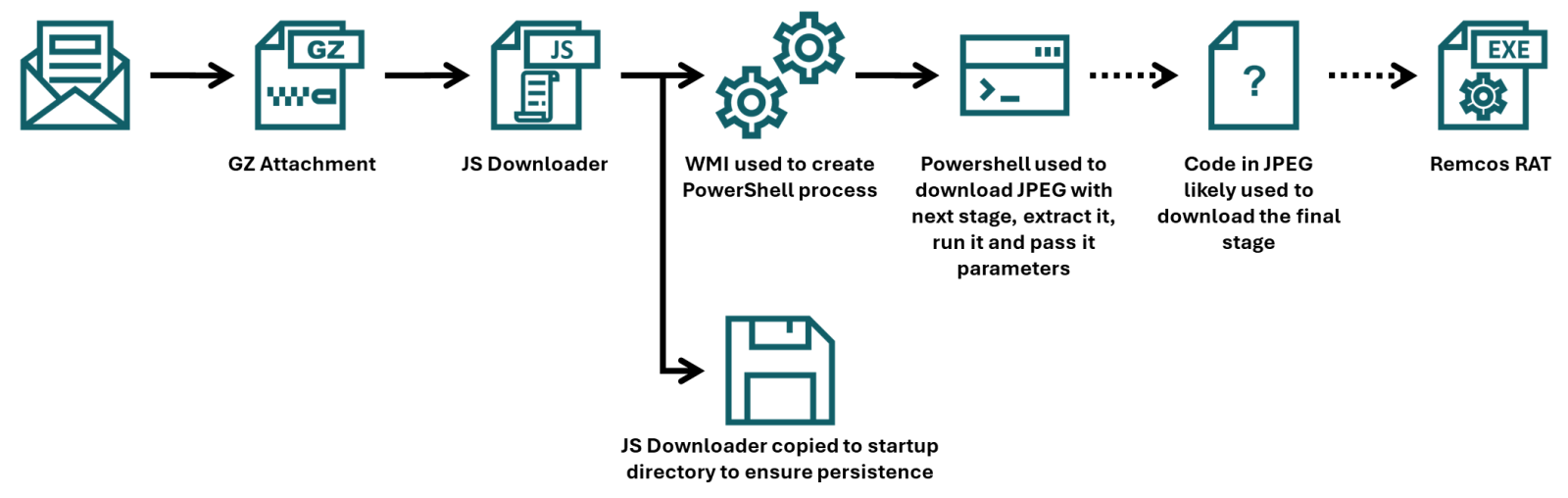
This article presents a detailed analysis of a recent malware campaign that uses advanced obfuscation techniques to evade detection. The infection chain begins with a JScript script attached to a phishing email and culminates with the download of Remcos RAT. The analysis focuses on the obfuscation techniques used and how to disassemble each stage of the attack.
Phishing Campaign and First Stage of Infection
The campaign was distributed via phishing emails impersonating a legitimate Czech company. Although the email contained credible visual elements, it failed DMARC/SPF checks, which would likely have resulted in it being quarantined by most mail servers.
The attached file was a JScript script with a GZIP wrapper. The initial file was noticeably large (1.17 MB), due to a simple but effective obfuscation layer. Most of the script (17,188 of 17,222 lines) consisted of an identical, redundant string.
JScript Analysis and Deobfuscation
By removing the redundant lines, the script was reduced to 34 lines of essential code (31 KB). Analysis of the remaining code revealed two main sections:
- Initial Persistence: The first 10 lines of the script attempt to achieve persistence by copying the JScript file to the operating system’s startup folder.
- Additional Obfuscated Code: The remaining 19 lines were protected with basic obfuscation techniques. Analysis from the end of the script up proved to be beneficial. A call to a PowerShell command was identified that used the “junk string inclusion” technique to hide its true purpose.
The script uses the WMI Win32_Process.Create method to run a hidden instance of PowerShell. This instance decodes the contents of the whatsamatta variable (Base64 encoded with UTF-8) and executes the resulting script using Invoke-Expression.
Second Stage Download: The Malicious Image
The second stage PowerShell script, once decoded and deobfuscated, contained a URL to download the next phase of the payload. The URL pointed to a file hosted on archive.org with a PNG extension (MSI_PRO_with_b64.png), but which was actually a JPEG file. This technique of hiding the payload within an image file (steganography) had already been observed in previous campaigns.
The PowerShell script is designed to extract a Base64 encoded string from the downloaded image and load it using reflection. Although the image file was no longer available at the time of analysis, the next stage of the infection could be examined by analyzing the parameters passed to the payload.
Final Stage: Remcos RAT
Analysis of the argsBase64 variable revealed parameters for the next stage, including another hidden URL. This URL (hxxps[:]//hotelseneca[.]ro/ConvertedFileNew.txt) contained the final stage of the payload: an executable file (EXE) encoded in Base64 and with inverted characters.
Upon decoding this file, the final payload was identified as a Remcos RAT sample. This finding confirms that the entire infection chain was designed to establish a remote access backdoor into the victim’s system.
Indicators of Compromise (IoCs)
URLs
hxxps[:]//ia600603[.]us[.]archive[.]org/13/items/msi-pro-with-b-64_202602/MSI_PRO_with_b64.pnghxxps[:]//hotelseneca[.]ro/ConvertedFileNew.txt
Files
- JS file (1st stage)
- SHA-1:
a34fc702072fbf26e8cada1c7790b0603fcc9e5c - SHA-256:
edc04c2ab377741ef50b5ecbfc90645870ed753db8a43aa4d0ddcd26205ca2a4
- SHA-1:
- TXT file (3rd stage – encoded)
- SHA-1:
bcdb258d4c708c59d6b1354009fb0d96a0e51dc0 - SHA-256:
b6fdb00270914cdbc248cacfac85749fa7445fca1122a854dce7dea8f251019c
- SHA-1:
- EXE file (3rd stage – decoded)
- SHA-1:
45bfcd40f6c56ff73962e608e8d7e6e492a26ab9 - SHA-256:
1158ef7830d20d6b811df3f6e4d21d41c4242455e964bde888cd5d891e2844da
- SHA-1:
References
Original source: See original article
- [1] https://isc.sans.edu/diary/Malicious+Script+Delivering+More+Maliciousness/32682/
- [2] https://isc.sans.edu/diary/Tracking+Malware+Campaigns+With+Reused+Material/32726/
- [3] https://learn.microsoft.com/en-us/windows/win32/cimwin32prov/win32-processstartup
- [4] https://isc.sans.edu/diary/Passive+analysis+of+a+phishing+attachment/29798
- [5] https://www.virustotal.com/gui/url/9cb319c6d1afc944bf4e213d0f13f4bee235e60aa1efbec1440d0a66039db3d5/details
- [6] https://www.virustotal.com/gui/file/656991f4dabe0e5d989be730dac86a2cf294b6b538b08d7db7a0a72f0c6c484b
- [7] https://www.virustotal.com/gui/file/1158ef7830d20d6b811df3f6e4d21d41c4242455e964bde888cd5d891e2844da