ESET researchers have discovered new activities of the Iran-aligned cyber espionage group MuddyWater (also known as Mango Sandstorm or TA450). This campaign primarily targets organizations in Israel and, in one confirmed case, Egypt, showing significant evolution in their technical and tactical evasion capabilities.
Key Aspects of the Campaign
Unlike previous operations, this MuddyWater campaign is more stealthy and sophisticated. ESET highlights the following points:
- Adoption of CNG Windows API: The group has integrated the Windows Crypto Next Generation (CNG) API, an unusual practice among Iranian groups and atypical in the overall threat landscape.
- New Backdoor MuddyViper: A new backdoor, MuddyViper, has been deployed using a loader called Fooder, which reflexively loads it into memory for execution.
- Detailed Technical Analysis: ESET provides an in-depth technical analysis of the tools used, including MuddyViper, Fooder, credential stealers CE-Notes and LP-Notes, browser data stealer Blub and reverse tunnels go-socks5.
- Avoidance of Interactive Sessions: Operators deliberately avoided hands-on-keyboard interactive sessions, which are traditionally noisy and error-prone.
MuddyWater Group Overview
MuddyWater has been active since at least 2017 and is one of the most active Iran-aligned APT groups, with ties to Iran’s Ministry of Intelligence and National Security. Its primary focus is cyberespionage, attacking government, military, telecommunications and critical infrastructure sectors in the Middle East and North America.
While MuddyWater’s operations are often “noisy,” recent campaigns, such as the one analyzed, demonstrate greater technical sophistication and precision in targeting. Previous campaigns such as Operation Quicksand (2020) and attacks on Saudi Arabia (2023) have been documented.
Victimology and Cooperation with Lyceum
The campaign was carried out between September 2024 and March 2025. Victims include organizations in Israel from the engineering, local government, manufacturing, technology, transportation, public services and universities sectors. A victim was also confirmed in Egypt’s technology sector.
An operational overlap was identified between MuddyWater and Lyceum (a subgroup of OilRig/HEXANE/Storm-0133) in January and February 2025. In this collaboration, MuddyWater gained initial access via spearphishing emails containing links to legitimate RMM software installers (such as Syncro), and then installed additional RMM tools. This suggests that MuddyWater could be acting as an initial access broker for other Iran-aligned groups.
Tactics, Techniques and Procedures (TTPs)
MuddyWater continues to use PowerShell and Go script-based backdoors. Initial access is typically achieved through spearphishing emails with PDF files containing links to RMM software installers hosted on free file-sharing services (OneHub, Egnyte, Mega). The group also deploys the VAX-One backdoor. The persistence of its well-known playbook makes it easier to detect and block, but the adoption of new tools indicates an evolution in its modus operandi.
Custom Toolset
ESET has documented a set of custom and previously unknown tools used in this campaign:
Loader Fooder
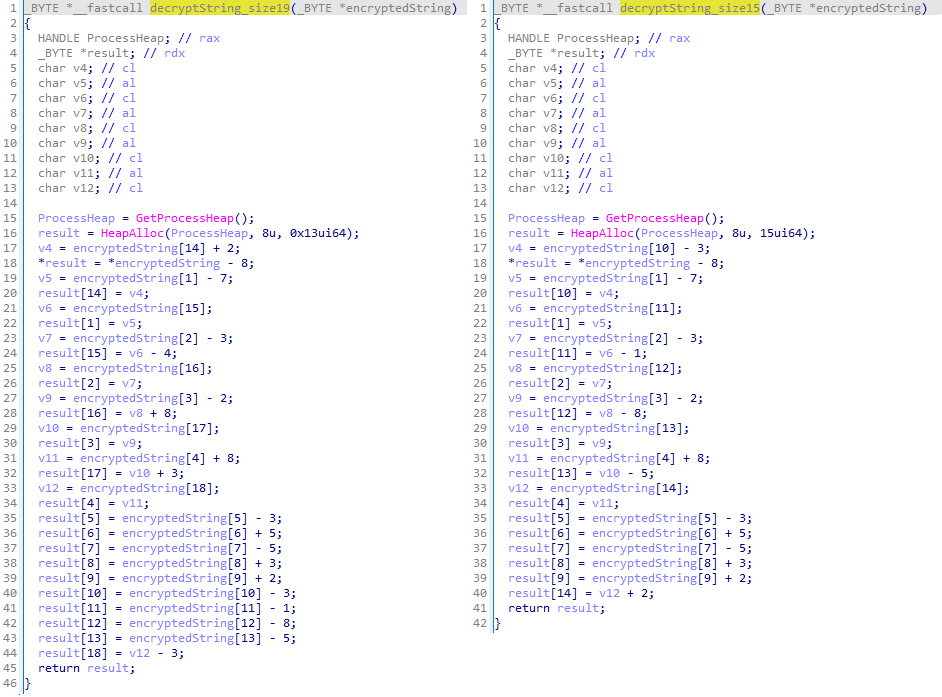
- 64-bit C/C++ loader designed to reflexively decrypt and load the in-memory embedded payload.
- Several versions impersonate the classic game “Snake” and incorporate delay logic inspired by the game, along with calls to the
SleepAPI, to evade automated dynamic analysis. - Its most common payload is the MuddyViper backdoor, but it also deploys HackBrowserData (an open source browser data stealer) and go-socks5 reverse tunnels.
Backdoor MuddyViper
- Undocumented C/C++ backdoor that allows the collection of system information, the uploading and downloading of files, the execution of commands, and the theft of Windows credentials and browser data.
- Runs exclusively in memory, loaded by Fooder, which explains the lack of obfuscation or string encryption.
- Maintains an extensive list of security tool processes for reporting to C&C.
- Set persistence through the Windows startup folder or scheduled tasks (e.g.
ManageOnDriveUpdater). - Supports 20 backdoor commands, including opening reverse shells and displaying a fake Windows Security dialog (command ID 805) to steal credentials.
CE-Notes Browser Data Theft
Browser data stealernamed by thece-notes.txtfile where it stores the stolen data.- Steals and decrypts encryption keys linked to Chromium-based browser applications (Chrome, Brave, Edge).
- Encrypts data collected with AES-CBC (CNG API) and stores it locally in
C:\Users\Public\Downloads\ce-notes.txtwithout direct exfiltration capability.
LP-Notes Credential Theft
Credential stealerC/C++ with the same design as CE-Notes, storing data inlp-notes.txt.- Its sole purpose is to induce victims to enter their Windows credentials by displaying a fake Windows security dialog (
CredUIPromptForWindowsCredentialsW). - Verify credentials in real time trying to log in.
- Uses string obfuscation techniques and dynamic resolution of API functions.
Blub Browser Data Theft
Browser data stealerin C/C++ (Blub.exe) that steals login credentials from Google Chrome, Microsoft Edge, Mozilla Firefox and Opera.- For Chromium browsers, kills processes, parses and decrypts encryption keys (DPAPI), and extracts credentials using SQL queries.
- For Firefox, decrypt credentials from
logins.jsonusingnss3.dll. - Store data locally in
file.txtunencrypted and with no exfiltration capability. - Performs process checks of security solutions (Avast, Norton) and adjusts their execution.
Reverse Tunnels go-socks5
- Collection of tools compiled in Go, based on public libraries (go-socks5, yamux, resocks), frequently used by MuddyWater.
- Internally called
ESETGO, they relay communication between the compromised machine and an encrypted C&C server via SSL/TLS, hiding the actual location of the C&C.
Conclusion
This campaign marks an evolution in MuddyWater’s operational maturity. The deployment of previously undocumented components such as Fooder and MuddyViper, along with game-inspired evasion techniques and reverse tunnels, demonstrates an effort to improve its capabilities. Although signs of operational immaturity remain, MuddyWater remains an important Iranian player, executing timely, effective, and increasingly difficult to defend campaigns. ESET will continue to monitor the evolution of its TTPs and strategic attacks.
References
Network Indicators of Compromise (IoCs)
- MuddyWater C&C Servers:
3.95.7[.]142(Amazon Data Services NoVa)35.175.224[.]64(Amazon Technologies Inc.)api.tikavod ot.co[.]il(51.16.209[.]105, Amazon Data Services Ireland)magically day[.]com(167.99.224[.]13, DigitalOcean, LLC)194.11.246[.]78(HosterDaddy Private Limited)processplan et[.]org(194.11.246[.]101, Administrator)212.232.22[.]136(HosterDaddy Private Limited)
- MuddyWater Staging Servers:
62.106.66[.]112(RIPE-NCC-HM-MNT, ORG-NCC1-RIPE)157.20.182[.]45(Hosterdaddy Private Limited)161.35.172[.]55(DigitalOcean, LLC)206.71.149[.]51(BL Networks)
Tools and Detections
- Fooder launcher:
OsUpdater.exe(Win64/MuddyWater.E) - Blub browser-data stealer:
Blub.exe,stealer.exe(Win64/MuddyWater.H) - CE-Notes browser-data stealer:
7d1e9726b5YZPYc.dll,fe197add74IVcQn.exe,vmsvc.exe(Win32/MuddyWater.B,Win64/MuddyWater.I) - LP-Notes credential stealer:
3a70e4c8c2IVcQn.exe(Win64/MuddyWater.C) - Mimikatz loader:
Dsync-es.exe(Win64/MuddyWater.F) - Fooder loader with HackBrowserData/go-socks5/MuddyViper: Various samples such as
App_chek.exe,steam.exe,antimage.exe,wtsapi32.dll,msi.dll,WinWin.exe,Launcher.dll,ncrypt.dll,WinWin(persist).exe(Win64/MuddyWater.G) - go-socks5 reverse tunnel: Numerous variants with names such as
0bff183a39ruQsY.dll,20d188afdcpfLFq.exe,dttcodexgigas.exe,ESETGO.exe,Revoke.dll,AppVs.exe(WinGo/TrojanProxy.Agent.D,WinGo/TrojanProxy.Agent.F)
MITER ATT&CK Frame
The techniques used in this campaign have been mapped against version 17 of the MITER ATT&CK framework.