Comfidentia Blog
Welcome to the Comfidentia blog, where we share knowledge about cybersecurity, technology, and best practices.
Welcome to the Comfidentia blog, where we share knowledge about cybersecurity, technology, and best practices.
Published on February 26, 2026

Cybersecurity researchers have revealed details about a new botnet loader called Aeternum C2, which uses a blockchain-based command and control (C2) infrastructure to resist takedown efforts. Instead …
Published on February 23, 2026
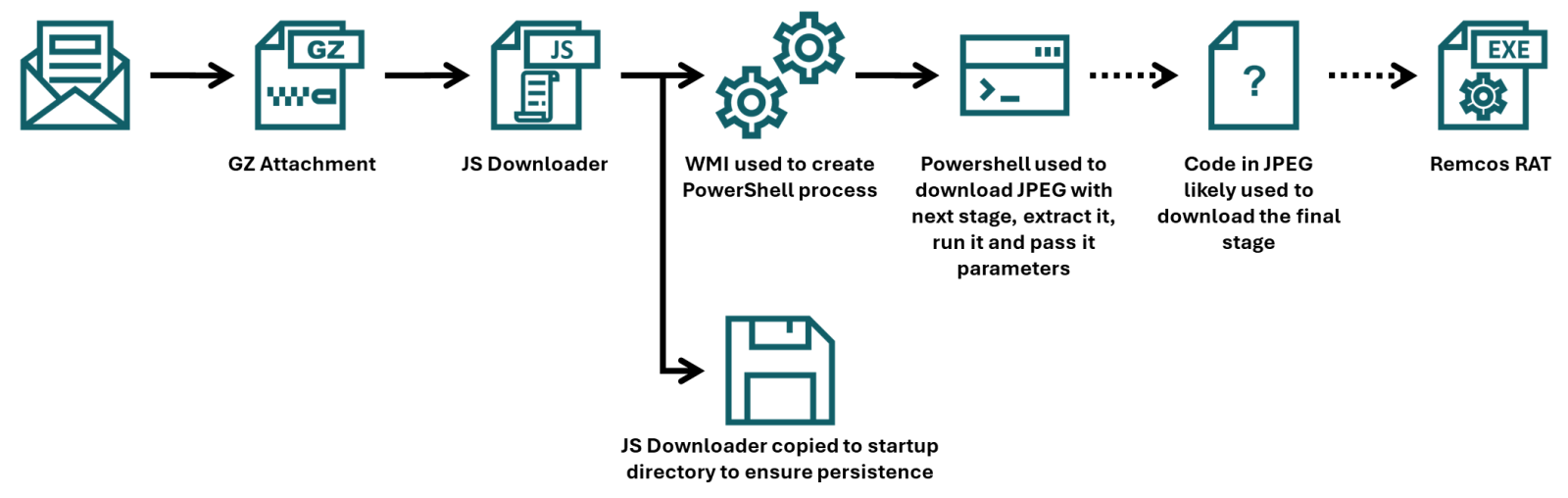
This article presents a detailed analysis of a recent malware campaign that uses advanced obfuscation techniques to evade detection. The infection chain begins with a JScript script attached to a …
Published on January 27, 2026

Cybersecurity faces a constant challenge: innovation from adversaries. The rise of offensive artificial intelligence (AI) is transforming attack strategies, making them harder to detect. Threat …
Published on January 26, 2026

Cloudflare has shared details about a recent Border Gateway Protocol (BGP) route leak incident that affected IPv6 traffic for 25 minutes. The incident caused significant congestion, packet loss, and …
Published on January 26, 2026

Fortinet has confirmed that it is working to fully fix a FortiCloud SSO authentication bypass vulnerability, following reports of new exploit activity on firewalls that had already been fully …